17 Ways to Keep Your WordPress Website Secure in 2025

WordPress powers over 43% of all websites worldwide, making it a prime target for hackers, malware, and brute-force attacks. Whether you run a personal blog, an eCommerce store, or a corporate website, securing your WordPress site is critical to protecting your data, customers, and online reputation.
Here’s a comprehensive list of 25 proven ways to keep your WordPress site secure — with real-world examples, recommended plugins, and best practices.
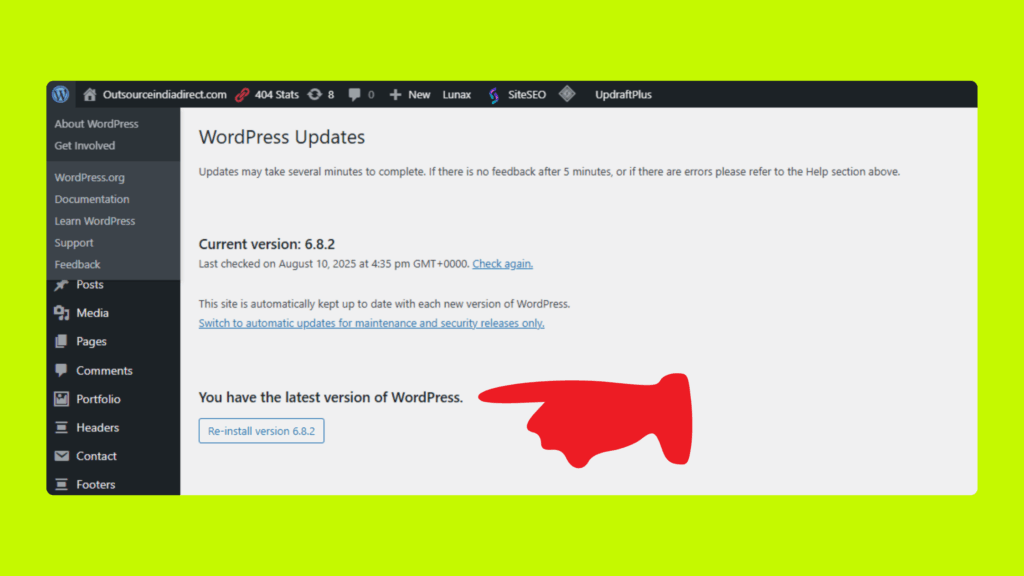
Keep WordPress Core Updated
Why it matters:
Running an outdated WordPress installation makes your site highly vulnerable. Hackers regularly exploit known flaws in older versions, making security breaches far more likely.
Best Practice:
- Always update to the latest WordPress version.
- Each update includes patches for security vulnerabilities discovered since the previous release.
Real-World Example:
In 2022, attackers exploited a cross-site scripting (XSS) vulnerability present in older WordPress versions, which allowed them to gain admin access and compromise websites.
How to simplify updates:
- Enable automatic updates in your WordPress dashboard.
- WordPress offers built-in tools to automatically apply most core, plugin, and theme updates, minimizing maintenance hassles and boosting protection.
- Check for updates weekly if not using auto-updates.
- Update themes and plugins as well, since vulnerabilities can exist there.
- Consider using a security plugin to alert you to outdated components.
Keeping your WordPress core updated is one of the simplest, yet most crucial, steps to secure your website against threats.
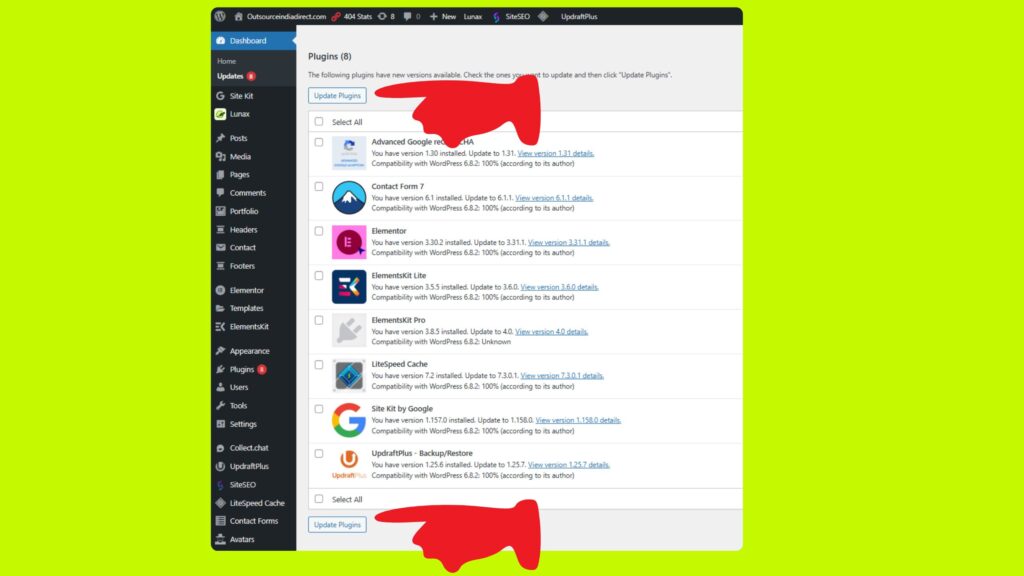
Update Themes and Plugins Regularly
Why it matters:
Outdated themes and plugins are widely recognized as the top source of WordPress security breaches—hackers frequently exploit old vulnerabilities that remain unpatched in unused or neglected components.
Best Practice:
- Regularly update every installed theme and plugin.
- Just like WordPress core, updates for themes and plugins often contain crucial security fixes.
- Delete any themes or plugins you do not use, rather than simply disabling them.
- Unused components can still present risks if vulnerabilities exist.
Real-World Example:
The Revolution Slider plugin (aka Slider Revolution) suffered a major security flaw exploited by attackers, compromising over 100,000 websites by enabling unauthorized access and data theft. This incident exemplifies the dangers of leaving plugins outdated.
How to simplify updates:
- Automate theme and plugin updates using tools like Easy Updates Manager. This plugin lets you configure automatic updates for all extensions, reducing manual effort and limiting the window of vulnerability.
- Review installed plugins and themes monthly.
- Only keep extensions that are actively maintained and necessary for your site.
- Consider security plugins that monitor the status and vulnerabilities of your site’s extensions.
Consistently maintaining updated and minimal plugins and themes is essential for safeguarding your WordPress site from common attacks.
Steps to Regularly Update Themes and Plugins (and Remove Unused Ones)
Follow these steps to keep your WordPress themes and plugins secure:
| Action | Navigation Path | Details / Tips |
|---|---|---|
| Log in to WordPress Dashboard | yoursite.com/wp-admin | Enter your username and password to access the dashboard. |
| Check for Updates | Dashboard → Updates | View all available updates for plugins, themes, and WordPress core. |
| Check Plugin Updates | Plugins → Installed Plugins | Plugins needing updates will show a notification badge. |
| Check Theme Updates | Appearance → Themes | Themes needing updates will display an update notice. |
| Update All Plugins | Plugins → Installed Plugins | Update individually by clicking Update now, or use Bulk Actions → Update. Tip: Make a backup before updating to avoid conflicts or data loss. |
| Update All Themes | Appearance → Themes | Click Update now for each theme with an update available. |
| Delete Unused Plugins | Plugins → Installed Plugins | Deactivate unused plugins, then click Delete. |
| Delete Unused Themes | Appearance → Themes | Activate your primary theme, then delete all others by selecting the theme and clicking Delete. |
| Automate Future Updates | Plugins → Add New | Search Easy Updates Manager, install, and activate it. Configure automatic updates for themes, plugins, and WordPress core. |
| Review Extensions Regularly | N/A | Set a monthly reminder to review and delete unused plugins/themes. Keeping only necessary, updated extensions reduces security risks. |
Use Strong, Unique Passwords
Why it matters:
Weak or reused passwords like “admin123” or “password” are easily cracked using automated tools and are among the first guesses hackers will try. Password-related breaches remain a major threat to WordPress sites, giving attackers instant access if they succeed.
Best Practices:
- Create passwords that are at least 12 characters long, mixing uppercase and lowercase letters, numbers, and special symbols for maximum strength.
- Never reuse passwords across multiple sites or accounts. Each login should have its own unique password.
- Avoid common words or obvious patterns. Hackers use dictionaries and guessing algorithms targeting easy passwords.
How to Ensure Strong Passwords:
- Use Trusted Password Managers
- Tools like LastPass and Bitwarden can generate secure, random passwords and store them safely so you don’t need to remember each one.
- Tools like LastPass and Bitwarden can generate secure, random passwords and store them safely so you don’t need to remember each one.
- Generate a Strong Password
- With either manager, use their built-in generator and set desired criteria (length, character types).
- With either manager, use their built-in generator and set desired criteria (length, character types).
- Update Your WordPress Passwords
- Go to “Users > Profile” in your dashboard.
- Click “Generate Password,” paste your newly created password, and save.
- Go to “Users > Profile” in your dashboard.
- Require Strong Passwords for All Users
- Use security plugins (e.g., Wordfence or iThemes Security) that enforce strong password requirements for all user roles.
- Use security plugins (e.g., Wordfence or iThemes Security) that enforce strong password requirements for all user roles.
- Set a Routine for Password Changes
- Schedule password updates at least twice per year and whenever team members change.
- Schedule password updates at least twice per year and whenever team members change.
Tips:
- Never share passwords over email or chat.
- Enable two-factor authentication if possible for added protection.
- Regularly audit user accounts, removing old or inactive users.
Using strong, unique passwords dramatically increases your site’s protection against unauthorized access. Password managers make it effortless to maintain strict security without the hassle of memorization.
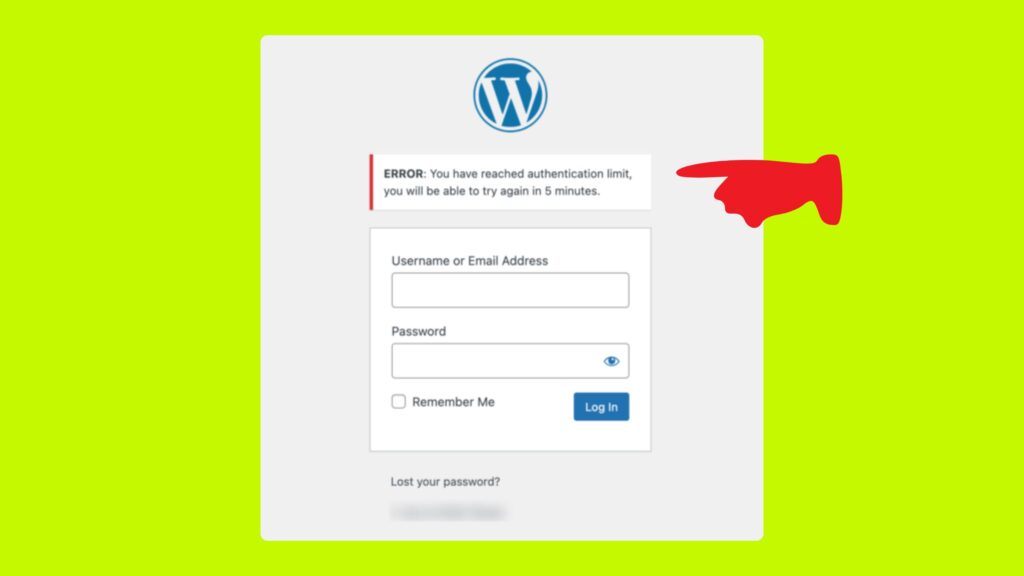
Limit Login Attempts
Why it matters:
Brute-force attacks flood your login page with thousands of password guesses until they break in. By default, WordPress does not restrict the number of login tries, leaving sites open to these attacks.
Best Practices:
- Limit failed login attempts per user/IP: After reaching your set threshold, lock the user out for a specified period to deter hacking bots.
- Monitor and block suspicious activity: Good plugins let you view attempted logins and block offending IP addresses.
How to Limit Login Attempts in WordPress
Recommended Plugins
- Limit Login Attempts Reloaded
- Features:
- Restricts number of login attempts (customizable).
- Locks users/IPs after exceeding allowed attempts.
- Supports all standard and custom login forms (including WooCommerce, XMLRPC).
- Offers logs, notifications, GDPR compliance, and premium features like cloud IP intelligence.
- Over 2.5 million active installations; easy to use with a high rating.
- Restricts number of login attempts (customizable).
- Features:
- WP Limit Login Attempts
- Features:
- Limits login attempts and temporarily blocks IP addresses.
- Adds captcha verification for extra protection after repeated failures.
- Obfuscates logged IPs for GDPR compliance.
- Limits login attempts and temporarily blocks IP addresses.
- Features:
Step-by-Step: Setting Up Login Protection
- Backup Your Site
- Always create a backup before installation or major security changes.
- Always create a backup before installation or major security changes.
- Install Plugin
- Go to Plugins > Add New in your WordPress dashboard.
- Search for Limit Login Attempts Reloaded or WP Limit Login Attempts.
- Click Install, then Activate.
- Go to Plugins > Add New in your WordPress dashboard.
- Configure Plugin Settings
- Navigate to Settings > Limit Login Attempts (or WP Limit Login).
- Set:
- Number of allowed attempts before lockout (e.g., 3-5).
- Lockout duration (default is 20min; you can increase it).
- Notifications—choose if you want email alerts for lockouts.
- GDPR compliance options.
- Number of allowed attempts before lockout (e.g., 3-5).
- Save changes.
- Navigate to Settings > Limit Login Attempts (or WP Limit Login).
- Optional: Advanced Protection
- Enable captcha (WP Limit Login Attempts).
- Consider premium features for geoblocking, advanced logging, and cloud protection (Limit Login Attempts Reloaded Premium).
- Add safelists/blocklists for IPs and usernames if needed.
- Enable captcha (WP Limit Login Attempts).
- Monitor Logs
- Regularly check plugin logs for failed attempts, blocked IPs, and notification reports.
- Regularly check plugin logs for failed attempts, blocked IPs, and notification reports.
Summary Tips
- Limit login attempts to 3–5 per session for normal users.
- Set a reasonable lockout period (20min–1hr), with longer bans after repeated offenses.
- Use captcha to deter bots after multiple failures.
- Always keep login protection plugins up to date!
Enabling login attempt limits is a simple but powerful defense against brute-force attacks. A well-configured plugin will automatically block hackers while keeping your site accessible for legitimate users.
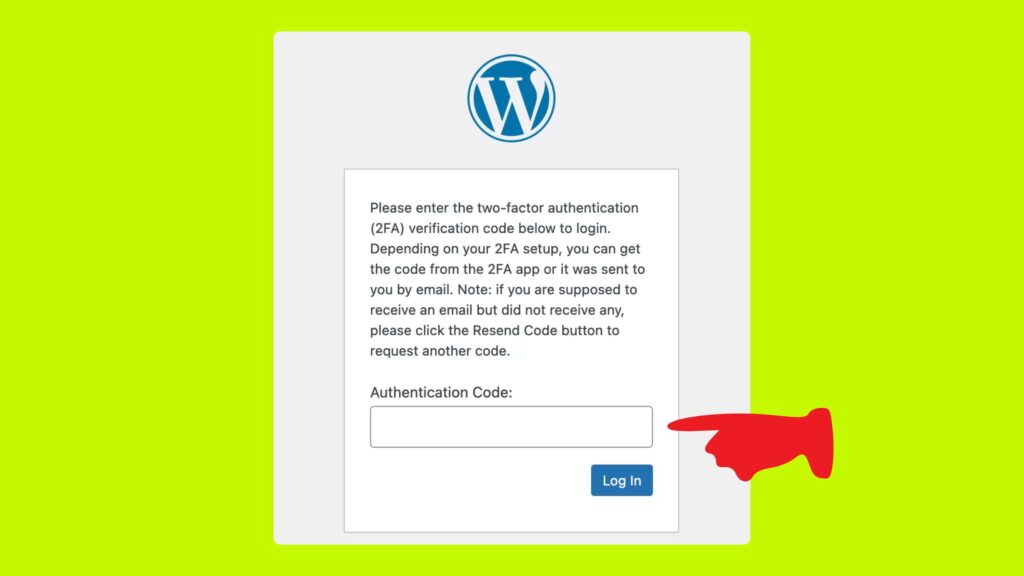
Enable Two-Factor Authentication (2FA)
Why it matters:
Even if your password is compromised, two-factor authentication (2FA) adds a crucial second step of verification, significantly reducing the risk of unauthorized access. It requires users to provide a time-sensitive code generated on a secondary device like a smartphone, adding an extra layer of protection beyond just a password.
How to Enable Two-Factor Authentication in WordPress
You can enable 2FA easily by using popular WordPress security plugins such as Wordfence or standalone 2FA plugins like Google Authenticator – WordPress Two Factor Authentication.
Steps to Enable 2FA Using Wordfence Plugin
- Backup Your Site:
Always take a backup before making major security changes. - Install and Activate Wordfence Plugin:
- In your WordPress dashboard, go to Plugins > Add New.
- Search for Wordfence Security.
- Click Install Now and then Activate.
- In your WordPress dashboard, go to Plugins > Add New.
- Enable 2FA in Wordfence:
- Navigate to Wordfence > Login Security in your dashboard menu.
- Under Two-Factor Authentication, toggle the switch to enable it.
- Select the user roles (usually Admins) for whom you want to enforce 2FA.
- Save the settings.
- Navigate to Wordfence > Login Security in your dashboard menu.
- Set Up the Authentication App:
- Download an authentication app on your smartphone, such as Google Authenticator, Authy, or Microsoft Authenticator.
- On your WordPress 2FA setup screen, scan the displayed QR code with your authenticator app.
- The app will generate a 6-digit time-sensitive code.
- Download an authentication app on your smartphone, such as Google Authenticator, Authy, or Microsoft Authenticator.
- Activate 2FA:
- Enter the 6-digit code from the app into WordPress to verify and activate 2FA.
- Download and save backup codes provided in case you lose access to your authenticator app.
- Enter the 6-digit code from the app into WordPress to verify and activate 2FA.
- Login with 2FA in Future:
- After entering your username and password, you will be prompted to enter the code from your authentication app to complete login.
- After entering your username and password, you will be prompted to enter the code from your authentication app to complete login.
Alternative: Enable 2FA Using Google Authenticator Plugin
- Install the Google Authenticator plugin via Plugins > Add New.
- Activate the plugin and follow its setup wizard to link with the Google Authenticator app.
- Scan the QR code and enter the verification code to enable 2FA for your user account.
Additional Tips
- Consider enforcing 2FA for all user roles with sensitive permissions.
- Regularly remind users to keep backup codes secure.
- Combine 2FA with strong, unique passwords for best protection.
Enabling two-factor authentication is a highly effective defense against unauthorized login attempts and should be an essential part of your WordPress security strategy.
Change the Default “admin” Username
Why it matters:
“Hackers almost always try ‘admin’ as a username first” because it is the default and most common admin username on many WordPress sites. Using “admin” makes it easier for attackers to execute brute-force or credential-stuffing attacks since they only need to guess the password. Changing the default admin username to something unique adds an important layer of security by making it harder for attackers to guess valid login credentials.
Step 1: Create a New Admin User with a Unique Username
- Log in to your WordPress dashboard.
- Go to Users > Add New.
- Fill in the user details:
- Choose a unique and hard-to-guess username (avoid anything like “admin” or obvious variations).
- Enter a strong password.
- Use an email address that you have access to.
- Choose a unique and hard-to-guess username (avoid anything like “admin” or obvious variations).
- Set the Role to Administrator.
- Click Add New User.
Step 2: Log Out and Log In as the New Admin User
- Log out of your current session.
- Log back in using the new admin username and password you just created.
Step 3: Delete the Old “admin” User
- Return to Users > All Users.
- Find the old “admin” username.
- Hover over it and click Delete.
- When prompted, attribute all content created by the “admin” user to your new user account, ensuring nothing gets lost.
- Confirm deletion.
Additional Tips:
- Never rename the “admin” user directly in the database or with plugins unless you fully understand the risks and backup your site.
- Always backup your WordPress site before making user or security changes.
- Use strong, unique passwords for all administrator accounts.
- Consider complementing this step with two-factor authentication to further protect admin access.
Changing the default “admin” username is a simple yet effective way to reduce the risk of hack attempts targeting WordPress administrator accounts.
Install a Security Plugin
Why it matters:
Security plugins provide comprehensive protection by scanning your WordPress site for malware, blocking suspicious traffic, and sending alerts about potential threats. They serve as your site’s first line of defense against hacking attempts, vulnerabilities, and malicious activity, minimizing risk and helping you respond quickly when issues arise.
Best Security Plugins for WordPress
- Wordfence Security
- Offers malware scanning, firewall protection, login security (including 2FA), real-time threat defense feed, and blocking of malicious IPs.
- Provides detailed security alerts and reports directly in your dashboard and via email.
- Includes options to monitor live traffic and detect ongoing attacks.
- iThemes Security
- Focuses on locking down common WordPress vulnerabilities including brute force protection, file change detection, strong password enforcement, and database backups.
- Comes with automated malware scanning and the ability to ban troublesome users.
- Integrates two-factor authentication and strong password enforcement.
- Sucuri Security
- Provides security auditing, malware scanning, blacklist monitoring, and post-hack cleanup tools.
- Includes a virtual firewall (WAF) option to block attacks before they reach your site.
- Offers website uptime monitoring and security notifications.
Use HTTPS with an SSL Certificate
Why it matters:
Using HTTPS with an SSL (Secure Sockets Layer) certificate encrypts data transmitted between your website and visitors, protecting sensitive information from interception or tampering. Besides enhancing security, Google favors secure websites in its search rankings, giving HTTPS-enabled sites a boost in visibility and trustworthiness.
How to Enable HTTPS on Your WordPress Site
Step 1: Obtain an SSL Certificate
- Free option: Use Let’s Encrypt, a popular free, automated, and open certificate authority that provides SSL certificates at no cost. Many web hosting providers support easy integration with Let’s Encrypt.
- Paid certificates: Available through your hosting provider or third-party vendors, often with additional warranties and support.
Step 2: Install the SSL Certificate
- Most hosts offer a simple way to install Let’s Encrypt or other SSL certificates via their control panel (e.g., cPanel, Plesk).
- If unsure, contact your hosting provider for assistance in activating SSL.
Step 3: Configure WordPress to Use HTTPS
- After installing SSL, your site URL needs to switch from http:// to https://.
- Update your WordPress Address and Site Address:
- In your WordPress admin dashboard, go to Settings > General.
- Change both the WordPress Address (URL) and Site Address (URL) to use https:// instead of http://.
- Save the changes.
Step 4: Use the Really Simple SSL Plugin to Simplify Settings
- Install and activate the plugin:
- Go to Plugins > Add New.
- Search for Really Simple SSL.
- Click Install Now, then Activate.
- The plugin automatically detects your SSL certificate and configures your website to use HTTPS, managing common issues such as mixed content (loading some HTTP assets on HTTPS pages).
- It also sets up redirects from HTTP to HTTPS to ensure visitors always access the secure version.
Step 5: Test Your Site’s HTTPS Configuration
- Visit your website and look for the padlock icon in the browser’s address bar.
- Use tools like SSL Labs’ SSL Test to verify your SSL certificate installation and check for vulnerabilities.
- Ensure all links, images, and scripts load using HTTPS to avoid security warnings.
Additional Tips:
- Make sure to update any hardcoded internal links or external services (like CDN, analytics, or payment gateways) to use HTTPS.
- Periodically renew your SSL certificate (Let’s Encrypt certificates typically renew automatically every 90 days).
- Keep backups and monitor your site after enabling HTTPS to catch any issues promptly.
Restrict File Editing from the Dashboard
Why it matters:
If hackers manage to gain access to your WordPress dashboard, one of the most dangerous things they can do is directly edit your theme and plugin files to insert malicious code. This internal file editing feature, accessible under Appearance > Theme Editor or Plugins > Plugin Editor, can be exploited to compromise your entire site.
Disabling file editing from the dashboard adds a crucial layer of protection by preventing anyone—even admins logged into WordPress—from modifying plugin and theme files directly through the interface.
How to Restrict File Editing in WordPress
- Access Your Site’s wp-config.php File
You can do this via:- Your web host’s file manager (e.g., cPanel, Plesk)
- An FTP/SFTP client
- SSH access, if comfortable with command line
- Your web host’s file manager (e.g., cPanel, Plesk)
- Edit wp-config.php
- Open wp-config.php, which is located in the root directory of your WordPress installation.
- Add the following line of code before the line that says /* That’s all, stop editing! Happy blogging. */:
- Open wp-config.php, which is located in the root directory of your WordPress installation.
define(‘DISALLOW_FILE_EDIT’, true);
- Save the Changes
- Save and upload (if using FTP) the updated wp-config.php file back to your server.
- Save and upload (if using FTP) the updated wp-config.php file back to your server.
What This Does
- The constant DISALLOW_FILE_EDIT set to true disables the built-in plugin and theme file editors.
- When this setting is active, the Appearance > Theme Editor and Plugins > Plugin Editor menus will be hidden or inaccessible in the WordPress dashboard.
- This measure helps prevent malicious actors or even accidental file edits that could break your site or introduce security vulnerabilities.
Additional Recommendations
- Combine this with strong admin passwords and two-factor authentication to reduce the risk of unauthorized access.
- Regularly back up your site before making changes to the wp-config.php file or other core files.
- Use security plugins that monitor file changes and alert you of suspicious activities.
Restricting file editing via the dashboard is a straightforward but effective security practice that helps protect your WordPress site from internal code tampering in case of compromised admin accounts.
Backup Your Website Regularly
Why it matters:
Regular backups are your safety net against data loss from hacking, server crashes, accidental errors, or other disasters. Having recent backup copies allows you to quickly restore your website to a previous clean state, minimizing downtime and damage.
Best Practices for WordPress Backups
- Backup Frequency:
Schedule backups frequently depending on how often your site changes—daily backups are ideal for active sites, while weekly may suffice for less frequent updates. - Store Backups Offsite:
Keep backup copies in secure, remote locations such as cloud storage (Google Drive, Dropbox, Amazon S3) or your backup provider’s servers to avoid losing backups if your server is compromised. - Test Your Backups:
Periodically verify that backups can be restored properly to avoid surprises when you need them most.
Recommended Backup Plugins for WordPress
- UpdraftPlus
- Features scheduled automatic backups of your entire site (files and database).
- Supports backup storage to multiple remote destinations.
- Easy restore process directly from the WordPress dashboard.
- Free and premium versions available with advanced features.
- BlogVault
- A premium backup service offering incremental backups, real-time syncing, and easy site migration.
- Includes a staging environment and support for restoring backups with one click.
- Cloud storage included with the service.
- VaultPress (part of Jetpack)
- Real-time cloud backups with automated daily scanning and one-click restores.
- Backup data stored securely on Automattic’s servers.
- Requires a paid Jetpack subscription plan.
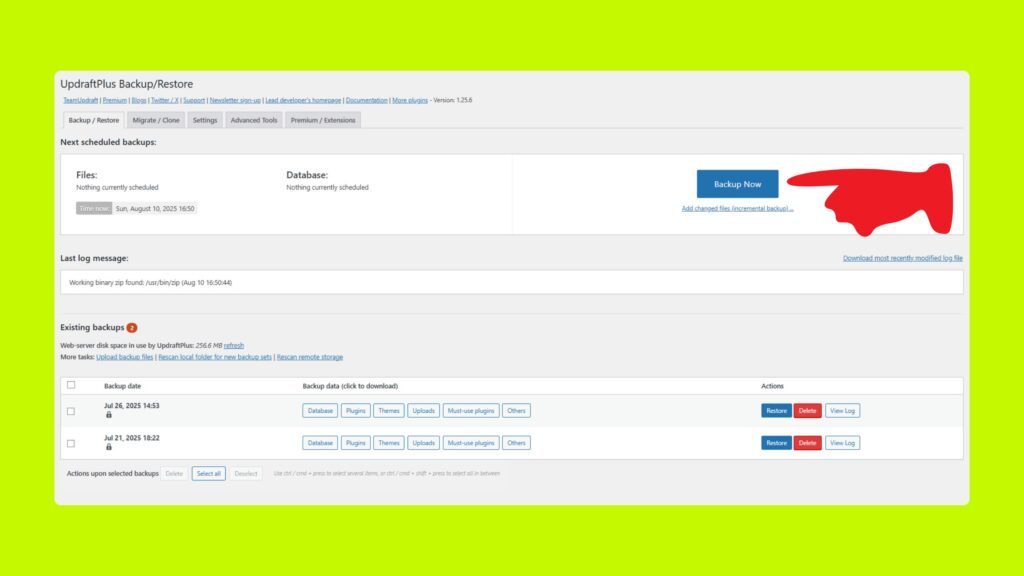
How to Set Up Backups Using UpdraftPlus (Example)
- Install and Activate UpdraftPlus
- Go to Plugins > Add New.
- Search for UpdraftPlus, install it, then activate.
- Configure Backup Settings
- Navigate to Settings > UpdraftPlus Backups.
- Set your backup schedule for files and database (e.g., daily or weekly).
- Choose remote storage options such as Google Drive or Dropbox and connect your account.
- Run Your First Backup
- Click Backup Now to create an immediate restore point.
- Restore When Needed
- Use the Existing Backups tab to restore your site to a prior state easily.
Protect Your wp-config.php File
The wp-config.php file is one of the most important and sensitive files in your WordPress installation. It contains critical configuration details, including your database credentials and security keys. Protecting this file from unauthorized access is essential to safeguard your site against hacking and data breaches.
Why it matters
If a hacker gains access to your wp-config.php file, they can obtain your database login information and other vital details to take full control of your website. Ensuring this file is well protected limits exposure to attacks.
Best Practices to Protect wp-config.php
1. Move wp-config.php One Directory Up
- By default, wp-config.php resides in the root folder of your WordPress files (usually public_html or www).
- You can move it one directory level above the root folder, which keeps it outside the publicly accessible web directory.
- WordPress will automatically look for it one level above if it’s not found in the root.
- This adds an extra layer of security, making it harder for attackers to access it via the web.
2. Restrict Access Using .htaccess Rules
Add the following code to your .htaccess file in the root directory of your WordPress installation to block all web access to the file:
<Files wp-config.php>
order allow,deny
deny from all
</Files>
This directive prevents any HTTP requests from viewing or downloading the wp-config.php file.
3. Set Proper File Permissions
- Set strict file permissions for wp-config.php to limit who can read or modify the file.
- Recommended permission: 400 or 440
- This means only the file owner (usually your server user) can read it, and others have no access.
- This means only the file owner (usually your server user) can read it, and others have no access.
- Avoid permissive settings like 644 which might allow other users on the server to read the file.
4. Disable File Editing in WordPress (if not done)
- Add this line to your wp-config.php file to disable built-in theme and plugin file editors:
define(‘DISALLOW_FILE_EDIT’, true);
This minimizes risks if unauthorized admin access is gained.
Additional Security Tips
- Regularly monitor your server logs for suspicious access attempts.
- Use security plugins that can alert you if wp-config.php is accessed or modified.
- Backup your wp-config.php file securely.
- Avoid displaying detailed error messages that might expose paths or sensitive info.
Protecting your wp-config.php file by moving it outside the web root, restricting access via .htaccess, and setting strict permissions is a fundamental step to harden your WordPress site’s security. Combined with other hardening techniques, it significantly reduces your risk of compromise.
Use a Web Application Firewall (WAF)
Why it matters:
A Web Application Firewall (WAF) acts as a security shield that filters and blocks malicious traffic before it reaches your WordPress site. It protects against a broad range of online threats such as SQL injection, cross-site scripting (XSS), brute force attacks, malware uploads, and zero-day vulnerabilities. By stopping attacks early, a WAF significantly reduces the risk of your site being compromised.
Best Cloud-Based WAF Options
- Cloudflare WAF
- Protects against OWASP Top 10 threats, account takeover attempts, and more.
- Features include managed rule sets regularly updated to protect against the latest vulnerabilities, customizable security rules, rate limiting of suspicious traffic, IP reputation blocking, and detailed security analytics.
- Works seamlessly with other Cloudflare services like DDoS protection, bot mitigation, and Content Delivery Network (CDN) for improved security and performance.
- Protects against OWASP Top 10 threats, account takeover attempts, and more.
- Sucuri WAF (CloudProxy)
- Combines WAF, Intrusion Detection System (IDS), and CDN to protect your site.
- Offers protection against SQL injections, XSS, Remote Code Execution (RCE), and protects from brute force and DDoS attacks.
- Includes virtual patching, performance acceleration through a global Anycast CDN, and continuous updates from a dedicated security research team.
- Enhances SEO by speeding up your website and enforcing HTTPS.
- Combines WAF, Intrusion Detection System (IDS), and CDN to protect your site.
How a WAF Works for Your WordPress Site
- Inspects incoming HTTP/HTTPS traffic in real-time.
- Filters out malicious requests based on security rulesets and threat intelligence.
- Blocks or challenges suspicious traffic before it can impact your server or site.
- Offers customizable options to tailor protection based on your site’s specific needs.
- Often includes logging and analytics for monitoring attacks and security posture.
Basic Steps to Use a WAF
- Choose a WAF Service:
Select a cloud-based WAF provider like Cloudflare or Sucuri that fits your needs and budget. - Sign Up and Configure:
Create an account and add your WordPress site to the service. This usually involves changing your domain’s DNS nameservers to route traffic through the WAF provider. - Enable WAF Protection:
Activate the firewall service within the provider’s dashboard. Use default managed rules initially to get immediate protection from common threats. - Customize Rules (Optional):
Configure specific rules such as rate limiting login attempts, blocking suspicious IP addresses, or creating custom security policies. - Monitor Traffic:
Review logs and analytics dashboards regularly to understand blocked threats and adjust settings as needed. - Combine with Other Security Measures:
Use the WAF alongside your WordPress security plugins, strong passwords, 2FA, and routine updates for layered defense.
Additional Tips
- Cloud-based WAFs are easy to set up without requiring changes to your WordPress code or hosting environment.
- They also improve site performance via CDN caching and global traffic routing.
- Be mindful of properly configuring firewall rules to avoid blocking legitimate users.
- Consider professional or enterprise plans if your site requires advanced protection and support.
Disable PHP File Execution in Certain Directories
Why it matters:
Disabling PHP file execution in specific WordPress directories, such as the uploads folder or wp-includes, helps prevent hackers from running malicious PHP scripts if they manage to upload them there. These directories typically only need to store files (images, documents, etc.) and should not execute PHP code. This simple security measure reduces the risk of server-side exploits and unauthorized code execution.
How to Disable PHP Execution via .htaccess
Add the following code to a .htaccess file inside the directory where you want to block PHP execution, for example, the wp-content/uploads or wp-includes folder:
<Files *.php>
deny from all
</Files>
This directive tells the web server to deny all access to any PHP file in that directory and its subdirectories, effectively preventing PHP scripts from running there.
Step-by-Step Instructions
- Access the directory on your server where you want to disable PHP execution (e.g., via FTP, SFTP, or your hosting file manager).
- Create or edit the .htaccess file in that directory.
- Paste the following code into the file:
<Files *.php>
deny from all
</Files>
- Save and upload the .htaccess file if using FTP/SFTP.
- Test the setting by trying to access a PHP file in that directory via a browser— access should be denied or show a 403 Forbidden error.
Recommended Directories for PHP Execution Restriction
- wp-content/uploads
- wp-includes
- Other writable directories that should only host static files
Additional Notes
- Be careful not to place this .htaccess file in the root directory of your WordPress site, as it will block PHP site-wide and break your website.
- This method works on Apache web servers; for Nginx, similar rules need to be applied differently.
- Combine this practice with other security measures like file and folder permissions and malware scanning for best results.
Monitor User Activity
Why it matters:
Tracking user activity on your WordPress site is crucial for security and accountability. By logging who logs in, what changes they make, and when these actions occur, you can quickly detect suspicious behavior, identify unauthorized changes, and audit user actions to keep your site safe and well-managed.
Recommended Plugin: WP Activity Log
WP Activity Log is a comprehensive, widely used plugin designed specifically for monitoring and logging detailed user and system activities on WordPress sites. It tracks a wide array of events, offering valuable insights and alerts to site administrators.
Key Features of WP Activity Log
- Detailed activity tracking: Logs user logins, logouts, failed login attempts, profile updates, and changes to posts, pages, plugins, themes, settings, and more.
- Real-time monitoring: View who is currently logged in and what actions they are performing.
- Notifications: Get instant email, SMS, or Slack alerts for important or suspicious changes.
- Reports: Generate customizable reports (HTML/CSV) for compliance and auditing.
- User session management: Force logoff for users directly from the dashboard.
- Integration: Supports activity tracking for popular plugins such as WooCommerce, Yoast SEO, WPForms, Gravity Forms, and others.
- Search & filter: Quickly find specific events using advanced filters by user, date, action, role, or IP address.
- Data storage: Optionally store logs in external databases or mirror them to log management services for scalability and security.
How to Set Up WP Activity Log
- Install the Plugin:
- Go to your WordPress dashboard.
- Navigate to Plugins > Add New.
- Search for WP Activity Log.
- Click Install and then Activate.
- Go to your WordPress dashboard.
- Activate License (for premium features):
- If using a premium version, enter the license key provided after purchase.
- Activate to unlock advanced features such as real-time alerts.
- If using a premium version, enter the license key provided after purchase.
- Access the Log Viewer:
- Go to WP Activity Log > Log Viewer.
- Here you can see a chronological list of all logged events with details like user, IP address, time, and description.
- Go to WP Activity Log > Log Viewer.
- Configure Events to Track:
- Navigate to WP Activity Log > Enable/Disable Events.
- Choose which activities you want to monitor (basic, geek, or custom levels of logging).
- Enable or disable specific types of events like content changes, user changes, plugin updates, etc.
- Navigate to WP Activity Log > Enable/Disable Events.
- Set Up Notifications:
- Configure email, SMS, or Slack notifications for critical events to stay informed in real time.
- Configure email, SMS, or Slack notifications for critical events to stay informed in real time.
- Monitor Logged-In Users:
- Use the Logged In Users page to see who is currently active and manage sessions.
- Use the Logged In Users page to see who is currently active and manage sessions.
Additional Tips
- Regularly review the activity logs to spot unexpected or unauthorized actions early.
- Combine user activity monitoring with other security measures such as strong passwords, two-factor authentication, and firewall protection for best results.
- Use reports for compliance audits and troubleshooting.
- Keep the plugin updated to benefit from new features and security improvements.
Hide WordPress Version
Why it matters:
Displaying your WordPress version number publicly can assist hackers in targeting your site with specific exploits against known vulnerabilities in that version. By hiding your WordPress version, you reduce the information available to potential attackers, making it harder for them to launch successful attacks based on version-specific security gaps.
How to Hide the WordPress Version Number
Add the following code snippet to your theme’s functions.php file:
php
remove_action(‘wp_head’, ‘wp_generator’);
This simple line of code removes the WordPress version meta tag from the <head> section of your site’s HTML output, effectively hiding the version number from browsers and bots.
Steps to Add Code to functions.php
- Access Your WordPress Dashboard:
- Go to Appearance > Theme Editor.
- Open functions.php:
- In the Theme Editor, find and open the functions.php file of your active theme (usually located under Theme Files).
- Add the Code:
- Scroll to the bottom of the file and paste the code snippet above.
- Save Changes:
- Click the Update File button to apply the change.
Additional Tips
- Be careful when editing functions.php; a syntax error can break your site. Always back up your website before making changes.
- Alternatively, use a site-specific plugin or a custom snippets plugin to add this code safely, avoiding direct theme file edits.
- Combine this with other security measures like updating WordPress regularly, using security plugins, and limiting information disclosure in headers and error messages.
Limit User Roles and Permissions
Why it matters:
Giving users full administrator rights when they don’t need them can seriously jeopardize your WordPress site’s security. Administrators have the highest level of access, including the ability to install or delete plugins, change themes, edit core files, add or remove users, and more. If an admin account is compromised, hackers gain full control of your site. Limiting roles and permissions to the minimum necessary for users helps prevent accidental or malicious damage and reduces the risk from compromised accounts.
Best Practices for Managing WordPress User Roles and Permissions
- Assign the least privilege necessary:
Only grant users the capabilities they need to perform their job. For example:- Content writers only need the Author or Editor roles.
- Shop managers (in eCommerce sites) have their own tailored roles.
- Administrators should be limited to trusted site owners or senior staff.
- Content writers only need the Author or Editor roles.
- Avoid using the default “admin” username and administrator role for routine tasks. Create custom users with lower privileges.
- Regularly audit user accounts and roles:
Remove inactive or unnecessary accounts. Downgrade roles if users no longer need elevated access. - Use plugins for more granular control:
WordPress’s default roles cover common needs, but you can use plugins like User Role Editor or Members to customize capabilities precisely. These plugins let you add or remove specific permissions without giving full admin rights. - Control who can create new users or assign roles:
Limit this ability to trusted administrators only to prevent privilege escalation.
How to Change User Roles in WordPress
- Log in to your WordPress dashboard.
- Navigate to Users > All Users.
- Find the user whose role you want to change and click Edit.
- In the Role dropdown, select the appropriate role with minimum necessary permissions.
- Click Update User to save changes.
Recommended Roles Overview
| Role | Capabilities Overview | When to Use |
| Administrator | Full control over the site | Trusted site owners, developers |
| Editor | Can publish and manage posts and pages | Content managers |
| Author | Can publish and manage own posts only | Content creators, bloggers |
| Contributor | Write posts but cannot publish | Guest authors, junior writers |
| Subscriber | Read-only access, manage their profiles | Registered users, customers |
Additional Tips
- Pair role limitations with strong passwords and two-factor authentication for each user for maximum security.
- Use activity monitoring plugins to keep track of user actions, helping quickly detect any unauthorized changes.
- Educate your team about the importance of respecting roles and security best practices.
Limiting user roles and permissions appropriately is a critical security principle that reduces risk, prevents accidental site damage, and protects your WordPress site from potential internal and external threats. It helps maintain control and accountability over who can do what on your site.
Use Login Captchas
Why it matters:
Adding a CAPTCHA to your WordPress login page is an effective defense against automated bots attempting brute-force attacks to guess usernames and passwords. CAPTCHAs require users to perform a task that is easy for humans but difficult for bots, such as clicking a checkbox or solving a simple puzzle. This verification step blocks malicious automated login attempts, protecting your site from hacking and spam.
Recommended Plugin: Advanced noCaptcha & invisible Captcha
Overview:
Advanced noCaptcha & invisible Captcha is a popular, free WordPress plugin that adds Google reCAPTCHA (including v2 and invisible v3 modes) to various forms on your site, including the login page. It is flexible and allows captcha on login, registration, password reset, comment forms, contact forms, WooCommerce, BuddyPress, bbPress, and more.
Key Features:
- Supports multiple Google reCAPTCHA versions (v2 “I’m not a robot” checkbox, invisible reCAPTCHA v3).
- Allows placing multiple captchas on the same page.
- Can apply conditional captcha, e.g., only on the login form if needed.
- Integrations with popular community and eCommerce plugins.
- Multisite user signups protection.
- Automatic detection and language adaptation.
Why Choose This Plugin:
- Easy to configure without coding.
- Enhances login security by reducing bot-driven login attempts.
- Doesn’t negatively impact user experience thanks to invisible captcha support.
- Free and regularly updated.
How to Add Login CAPTCHA with Advanced noCaptcha & invisible Captcha
- Install and Activate the Plugin
- From your WordPress dashboard, go to Plugins > Add New.
- Search for Advanced noCaptcha & invisible Captcha.
- Click Install Now, then Activate.
- Get Google reCAPTCHA API Keys
- Visit Google’s reCAPTCHA website.
- Register your site and obtain the Site Key and Secret Key for the reCAPTCHA version you wish to use.
- Configure the Plugin
- Go to Settings > Advanced noCaptcha & invisible Captcha in your WordPress dashboard.
- Enter your Site Key and Secret Key.
- Enable captcha on the Login Form option (and others if desired).
- Adjust additional settings such as the type of captcha, error messages, and appearance.
- Save Settings and Test
- Save your changes.
- Log out and open your site’s login page to verify that the CAPTCHA appears and functions properly.
Additional Tips
- Consider enabling invisible reCAPTCHA (v3) to reduce friction for users while keeping the site protected.
- Combine CAPTCHA with other login security measures like limiting login attempts, two-factor authentication, and strong passwords for layered security.
- Regularly update the plugin and your API keys.
- Monitor login attempts and security logs for suspicious activity.
